I'm happy to announce that we've just released v0.11 of both mitmproxy and pathod. This release features a huge revamp of mitmproxy's internals and a long list of important features. Pathod has much improved SSL support and fuzzing.
Our thanks to the many testers and [contributors](https: //github.com/mitmproxy/mitmproxy/blob/master/CONTRIBUTORS) that helped get this out the door. Please lodge bug reports and feature requests here.
Mitmproxy Changelog
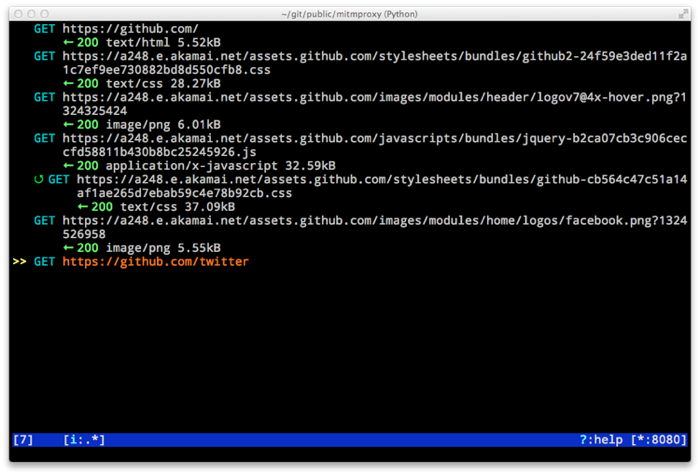
- Performance improvements for mitmproxy console
- SOCKS5 proxy mode allows mitmproxy to act as a SOCKS5 proxy server
- Data streaming for response bodies exceeding a threshold (bradpeabody@gmail.com)
- Ignore hosts or IP addresses, forwarding both HTTP and HTTPS traffic untouched
- Finer-grained control of traffic replay, including options to ignore contents or parameters when matching flows (marcelo.glezer@gmail.com)
- Pass arguments to inline scripts
- Configurable size limit on HTTP request and response bodies
- Per-domain specification of interception certificates and keys (see --cert option)
- Certificate forwarding, relaying upstream SSL certificates verbatim (see --cert-forward)
- Search and highlighting for HTTP request and response bodies in mitmproxy console (pedro@worcel.com)
- Transparent proxy support on Windows
- Improved error messages and logging
- Support for FreeBSD in transparent mode, using pf (zbrdge@gmail.com)
- Content view mode for WBXML (davidshaw835@air-watch.com)
- Better documentation, with a new section on proxy modes
- Generic TCP proxy mode
- Countless bugfixes and other small improvements
Pathod Changelog
- Hugely improved SSL support, including dynamic generation of certificates using the mitproxy cacert
- pathoc -S dumps information on the remote SSL certificate chain
- Big improvements to fuzzing, including random spec selection and memoization to avoid repeating randomly generated patterns
- Reflected patterns, allowing you to embed a pathod server response specification in a pathoc request, resolving both on client side. This makes fuzzing proxies and other intermediate systems much better.